

Work safely in the cloud with Chrome
Fast, secure and cloud-native. A powerful, simplified operating system combined with the Chrome Enterprise license keeps your business safe in the cloud.
Chrome Browser
Providing a trusted, consistent browsing experience across devices, with built-in protections, centralized management, and enterprise-wide control for IT admins.
Chrome OS
A cloud-native operating system that’s secure by design, simple for IT to manage, easy for employees to use and ready for enterprises to deploy worldwide.
Secure by design
- Built-in security with multilayered approach
- Regular updates every 6 weeks (and every 2 to 3 weeks for security patches)
- AI-driven threat detection with Safe Browsing and Google Play Protect
All your trusted apps
- Work securely with cloud-based G Suite apps through Chrome Browser
- Use legacy apps through virtualisation with VDI solutions from Citrix®, VMware, and others
Safe money
Chrome for your daily productivity
Chromebooks
A system that boots up in seconds and the overall computer runs smooth. Setup requirement is minimal. A user only has to flip open the Chromebook and login into a Google account.
Maintenance is also hassle-free unlike other operating systems like Windows. Google also updates the OS regularly and automatically. Chrome OS also has a build-in anti-virus protection. There is also no need for regular updating of several apps unlike in OS X because Chrome OS apps are stored in a cloud.

Enterprise License manages your Chrome device
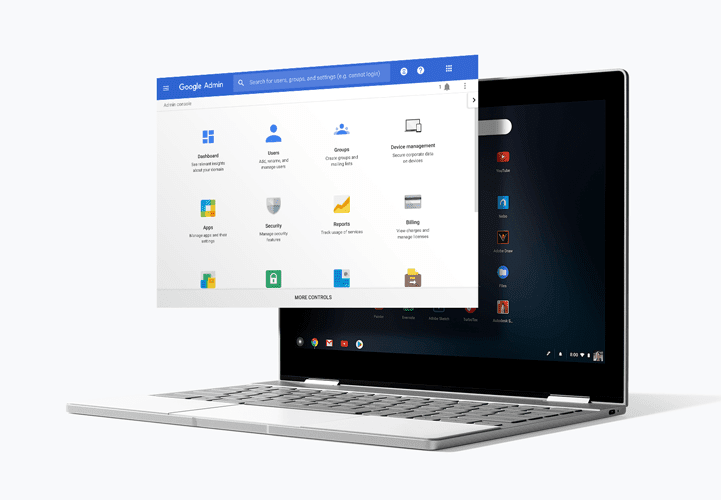
Granular policy controls for your devices
- Users Policies
- Devices Policies
- Fleet Management
- Bulk Printer Configuration
- Access and Permissions Management
Manage users’ cloud activity across all devices
- Stop unauthorized access if a device is lost or stolen with remote lock.
- Ensure compliance with all employees from day one.
- Curate your own app store for employees to use.
- Whitelist browser extensions and avoid potentially harmful applications.